Using Virtual Networks To Secure Your Resources

 In this post, I'm going to highlight one of Stackery's more interesting nodes. The Virtual Network node provides a powerful mechanism for securely deploying resources inside a private network.
In this post, I'm going to highlight one of Stackery's more interesting nodes. The Virtual Network node provides a powerful mechanism for securely deploying resources inside a private network.
Why Do We Need Private Networks
As an example of what a private network enables, let's take a look at how to secure a database. When you connect to most databases, you provide a username and password to gain access. But some databases are easy to set up without requiring user credentials to gain access. As an example, hundreds of millions of passwords were recently leaked via an unprotected database accessible on the internet. It is unfortunately too easy to misconfigure database security settings when initially setting up the database or when updating or changing settings.
But let's say you have set up a database with proper credential-based access controls. This sounds like a good amount of security by itself. If you don't have the proper credentials, you won't be able to access the database. What could go wrong?
Unfortunately, relying only on credentials for database security presents many problems. If your database is accessible on the internet people will find ways to either break into it or cause other nasty problems. Many databases do not have effective countermeasures for brute force password attacks. You can easily find articles, like this one, demonstrating how to use common tools to perform brute force password attacks on databases.
But even if you use a strong password with a database that uses proper password hashing and salting techniques to prevent brute force attacks from being successful, you can still end up overloaded via a denial of service attack where many malicious clients attempt to connect to your database simultaneously and exhaust available resources.
The solution to these problems is simple: put your databases inside private networks that only your services can access.
Stackery Virtual Network Node
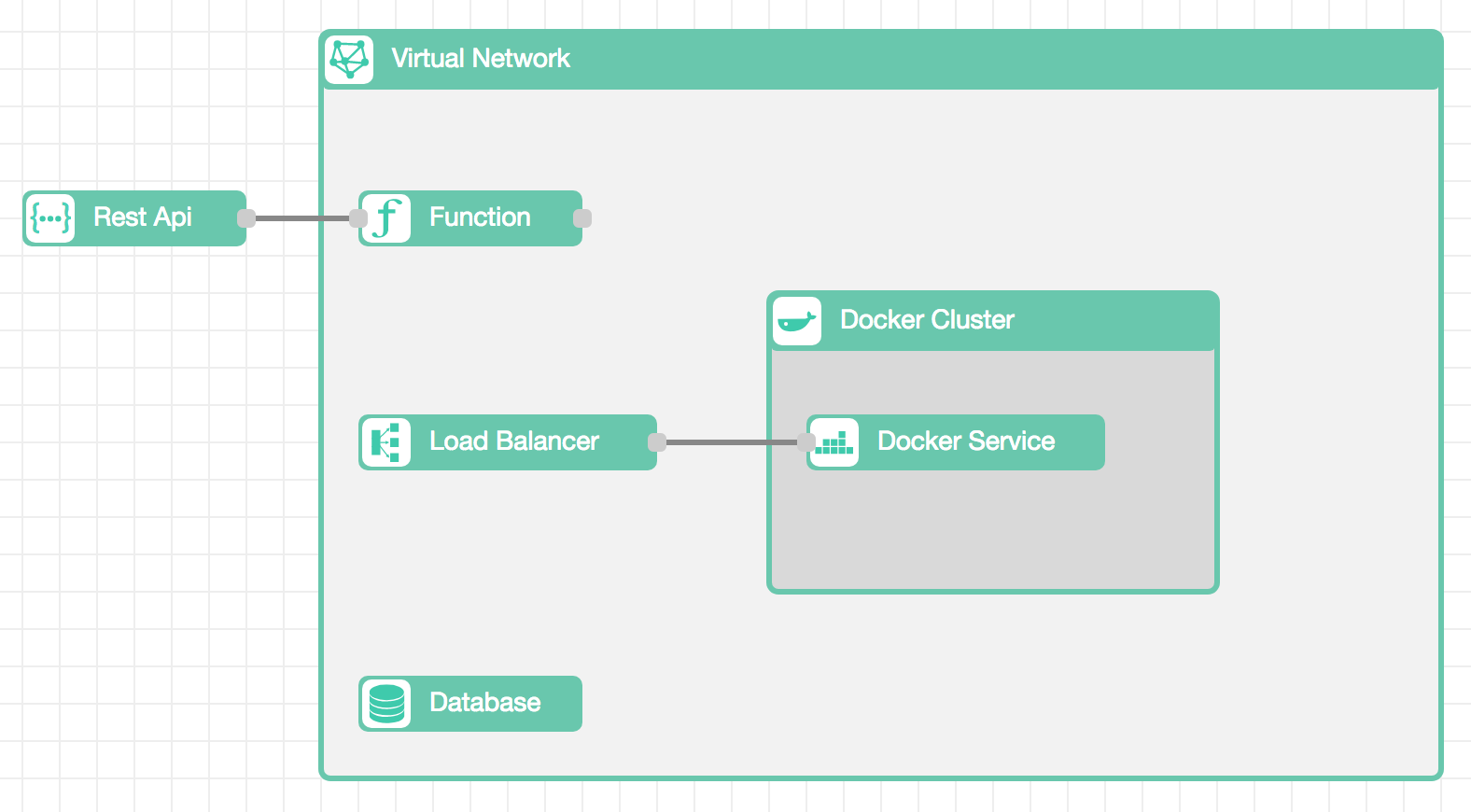
Stackery's Virtual Network node makes it easy to place your databases and services inside private networks. When you add a Virtual Network node, Stackery creates a Virtual Network with private and public subnets. Resources placed in public subnets can be accessed from the internet, while resources placed in private subnets can only be accessed by other resources within the same Virtual Network.
As an example, when you place a Database node in the Virtual Network, the Database is provisioned inside a private subnet. The same is true of Docker Task nodes. But when you place a Load Balancer in the Virtual Network, the Load Balancer is provisioned inside a public subnet. This allows internet traffic to reach the Load Balancer, which then routes traffic to Docker Services running in private subnets of the same Virtual Network. For serverless use cases, Function nodes can also be placed inside Virtual Network nodes to ensure they execute within a private subnet of the Virtual Network.
Stackery Best Practices
The Virtual Network node is another example of how Stackery helps engineers go from concept to implementation using industry best practices. Under the covers, a Virtual Network node is implemented using over a dozen AWS resources. But the magic of Stackery ensures the Virtual Network and all the resources placed inside it are properly networked to provide the right level of security.
Related posts

